Using a VPN Within WSLg
Learn how and why you can use a VPN within WSLg with a graphical user interface to turn it on and off

Last Updated: January 11th, 2022
By: Steve
Contents
WSLg – the latest incarnation of Microsoft’s Windows Subsystem for Linux includes the ability to run graphical Linux applications. At present it’s only available in Windows 11 or a Windows 10 Insider Build. I’m led to believe though that it will be available in standard Windows 10 at some point.
But if you’re wondering if you can use a VPN within WSLg then the simple answer is yes you can and it’s incredibly easy and works incredibly well. And the addition of the graphical interface makes managing your VPN considerably easier too.
I’ve looked at running a VPN in WSL before, using PureVPN and the command line. This post will dive into using my preferred VPN – PrivateInternetAccess – on WSLg and show you how fast it is, even under WSLg and how to set it up.
Why Use A VPN Under WSLg
There’s a few reasons I can think of why you might want to do this, you may think of others and if you do please leave a comment below and let me know.
- Browse the web safely with a ‘VPN Kill Switch’ but still access local services from Windows.
- Test or run a service within WSLg from the outside world (PrivateInternetAccess supports port forwarding)
- Hide your location within WSLg but keep Windows in your actual location
- Run 2 instances of PrivateInternetAccess – 1 in WSLg and 1 in Windows and appear from 2 different places, neither of which are where you actually are!
- Because you can…
Install Private Internet Access VPN in WSLg
The easiest way to do this is to use a browser within WSLg itself. By the way, I’ve not written about it yet but WSLg is a quantum leap forward in running WSL on Windows. Linux GUI apps seem to run at almost native speeds. But that’s for another article 🙂
You can download Private Internet Access from this link.
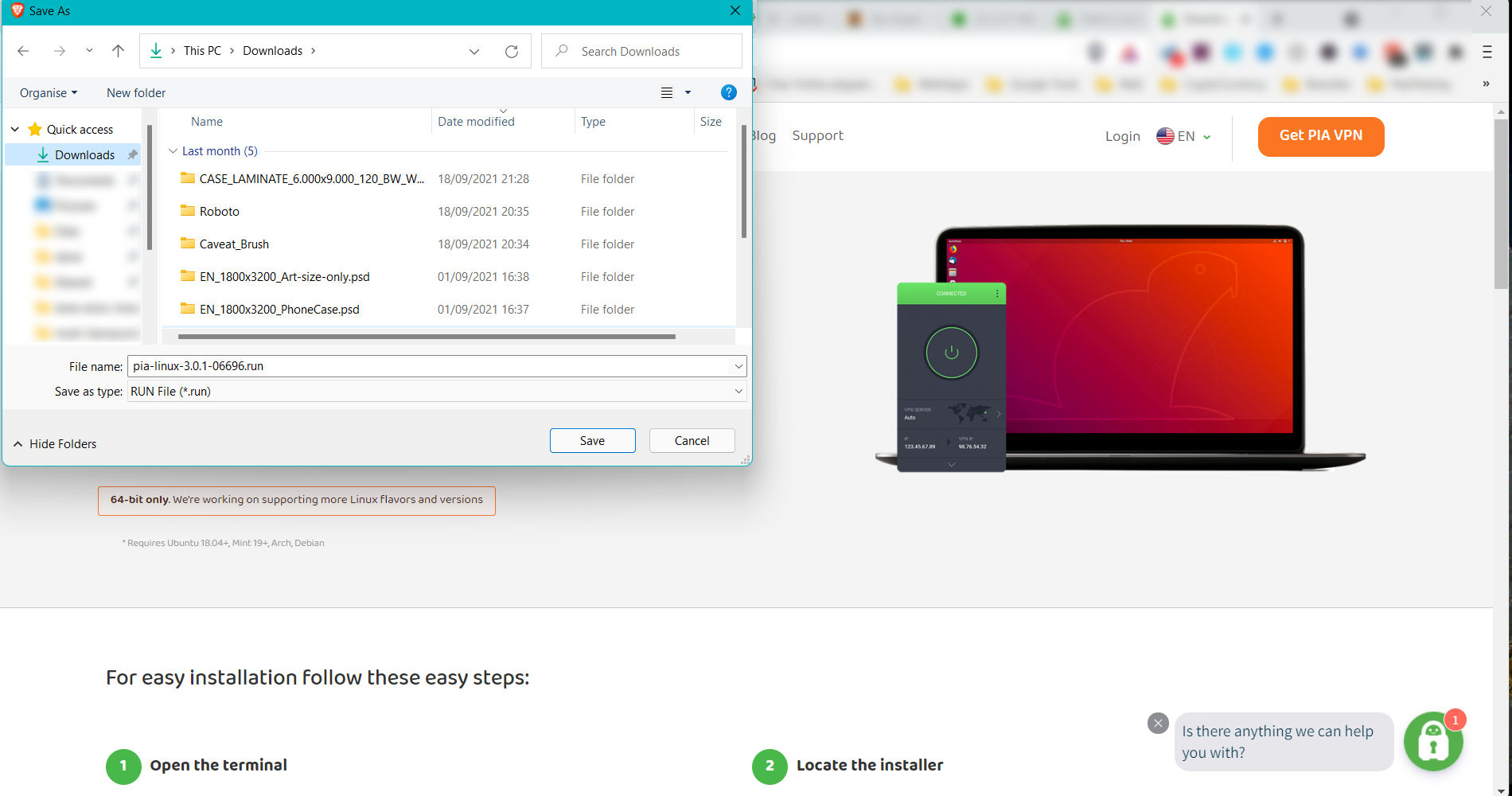
It’s worth installing Firefox (or Brave) in WSLg to download PrivateInternetAccess straight into your WSLg installation. But if you don’t want to, you can use your Windows browser to download the PIA client and then copy it across to your WSLg installation. If you do this, you can copy from Windows file system to WSLg using the command;
$ cp /mnt/c/Users/<username>/Downloads/pia* ~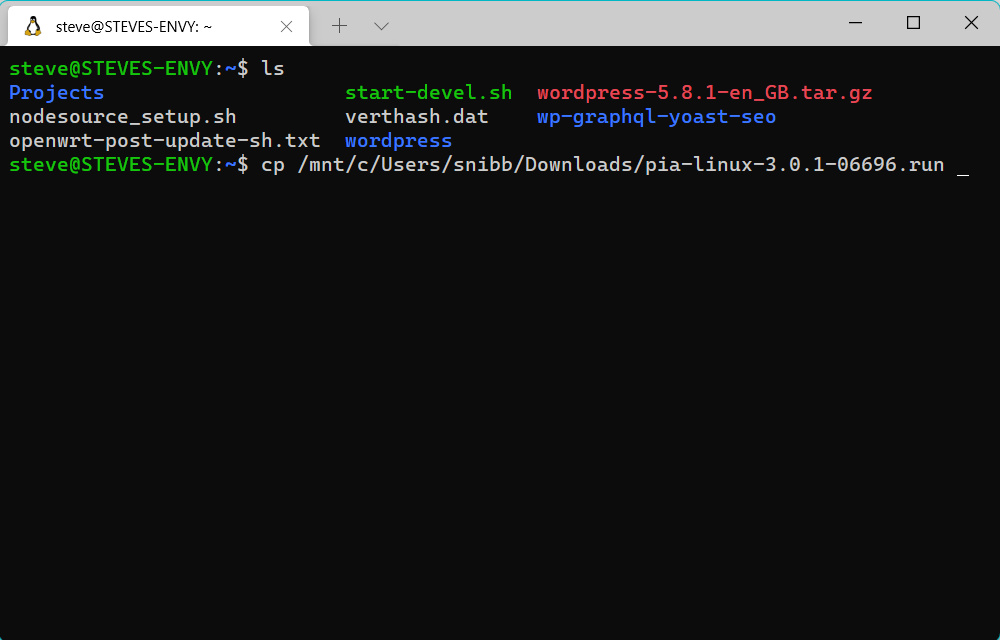
This will copy the .run file to your WSL home directory and from there you can simply issue the command;
$ ./pia-linux-3.0.1-06696.runThis will install PrivateInternetAccess into your WSLg installation. After it’s installed, it will automatically launch the graphical client. But on my machine this did take about 10 seconds the first time around. It was almost instant the second time.
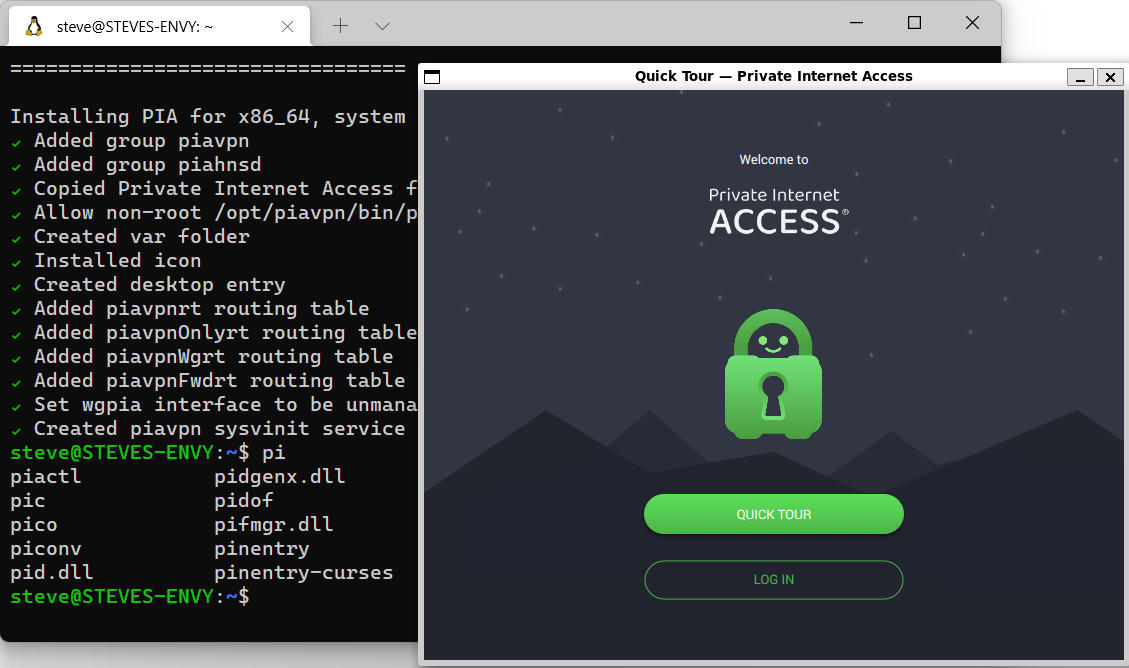
Logging In To PIA in WSLg
You’ll need an account with PrivateInternetAccess of course, but I’ve assumed you already have one – if not you’ll need to subscribe to PIA in order to use it on a computer. They do offer a 7 day trial on iOS or Android devices but not on computers.
I’ve joined PIA for 3 years (about 6 months ago) so I know that it works and is incredibly reliable.
Pro Tip: Your Password Manager (such as LastPass or SafeInCloud) can be used to login to your Private Internet Access WSLg screen. This is because the clipboard is shared across Windows 11 and WSLg seamlessly. Open up your password manager, copy the username and paste it into the username field on Private Internet Access client. Do the same with your password.
Once you’re logged in, you configure Private Internet Access through the GUI in exactly the same way as you would on a normal Linux computer, or indeed, Windows 10/11.
I usually switch to the Wireguard protocol as it connects almost instantly and seems to offer more throughput. I am however assuming that Wireguard is as secure as OpenVPN protocol – which I suspect it is since it’s very popular.
Connecting WSLg Via VPN
Once configured, you can then connect to any of the locations that you wish to. This is pretty cool because you can use the WSLg instance to connect to some place while your main Windows environment remains on the LAN. Or you can connect your WSLg instance to one location and your Windows location to another using the PIA client in WSLg and Windows at the same time.
The images below show this working with Private Internet Access graphical client in WSLg and Windows;
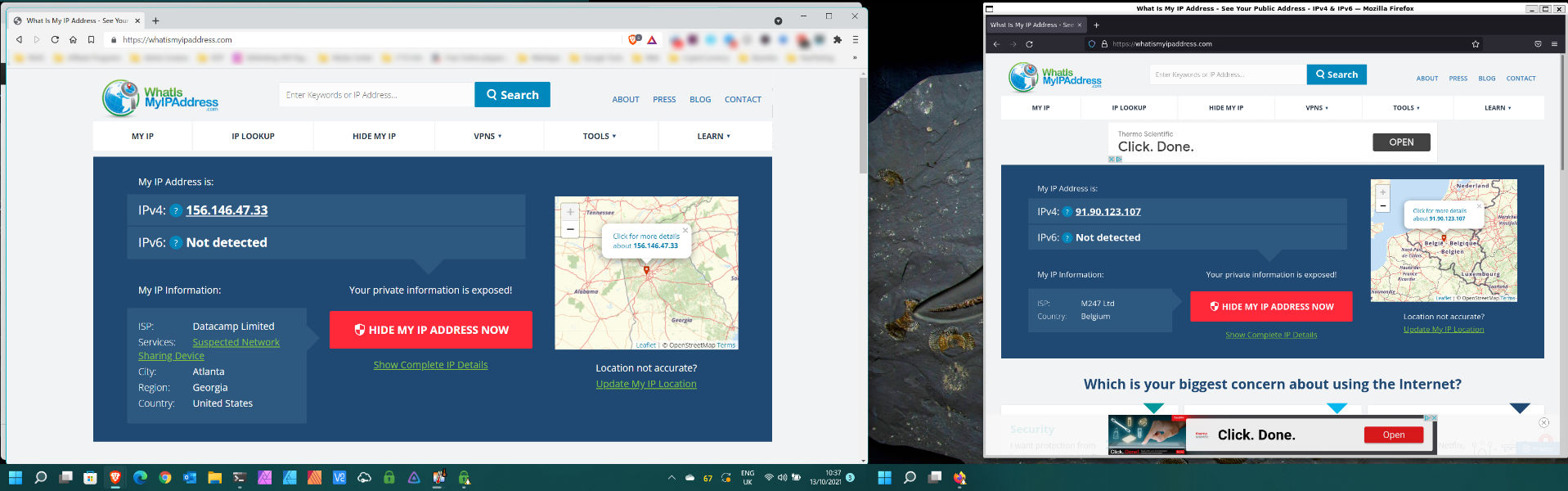
But PIA makes it look like I am 🙂
Use PIA On WSLg To Share A Linux Based Internet Service
PrivateInternetAccess allows you to setup one port forward. It’s a little bit hit and miss in that you may not get the same port forwarded each time you use it so it only really makes sense for development work – but if you’re wanting to show a colleague a progress mock up or demo to a customer before going live, it could be useful.
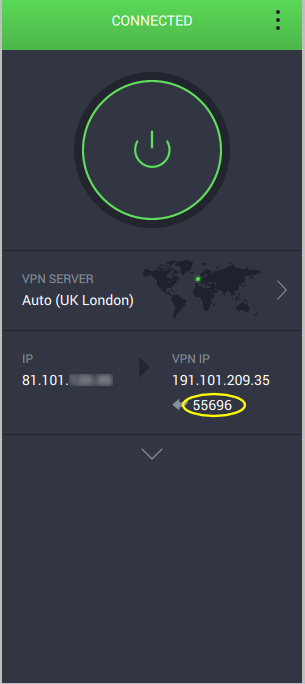
To use it, simply switch the option on in the PIA configuration and re-connect. Then you’ll see the port you’ve been allocated just underneath the IP address you’ve been given. The picture below shows you where to look – I’ve highlighted it with the yellow elipse.
Is PIA Under WSLg Fast Enough?
You might be thinking that using PIA with the GUI under WSLg would be horrendously slow. It’s not though. But, your mileage may of course vary depending on which VPN server you connect to and which protocol you use. It’ll also vary depending on how many people are using it at the same time you are. So many variables.
But for my test, I connected to a London server since that’s the same country as me, and ran a SpeedTest.net test. I’m on 100Mbit fibre here and generally see SpeedTest results around the 102MBiits/s. As you can see from the screenshot below, I’ve dropped about 4-5% of my top speed. Not bad considering that’s got WSLg overhead and PIA overhead…

Ad-Blocking Features
Ironic that I would talk about this feature when this site relies almost entirely on ad revenue to pay for hosting (though if you like the content and use Brave Browser you can ‘tip’ us using the Brave Rewards triangle at the top of your browser). But it’s a feature of PIA if you’re interested in it (though it’s free with Brave Browser too) and you’ll notice there’s no ads on that SpeedTest result.
Personally I generally leave ads running as they help pay for sites, but equally I understand why people wouldn’t.
Troubleshooting
The only issue I’ve had is that the PIA-Daemon doesn’t start automatically when you restart your machine or WSL instance. This is largely to be expected since WSL still uses its own init system and doesn’t, to my knowledge, allow us to hook into that to start processes at ‘boot’ time.
You can of course use SystemD-Genie to get around this. Or in my case I just issue the following command when I want to use PIA in WSLg;
$ sudo service piavpn startIt should start with that.
My Personal Experience With PIA and WSLg
So I’ve only been on Windows 11 a few days at the time of writing this. The scaremongering on YouTube isn’t particularly accurate, although there are some odd quirks with 11 that weren’t present in 10. Such as the Search feature often just not bothering to work at all.
I’ve also had trouble with WSLg just not starting automatically when Windows reboots, resulting in an annoying error when you first open up the terminal. It says that it can’t open \\wsl$\Ubuntu-20.04\home\steve and then fails. The only solution I’ve found was to open PowerShell and start wsl manually with the ‘wsl’ command. It doesn’t always do it though either, so that’s annoying.
WSLg has proven to be very fast, and largely seamless when running graphical applications. I did appear to confuse it when I installed a Debian instance and wanted to try that as well as my Ubuntu instance. I’m not sure if that’s a bug or by design. But the whole lot broke and I had to reboot to get any GUI applications working again.
PIA on WSLg, on Ubuntu is solid. I couldn’t get it to work on my Debian install due to the above error, so I haven’t tried it. However, there is one potential flaw;
The kill switch works only while PIA client is running when using it in WSLg. This means if you’re using it for anything unattended, and the client dies for some reason, your traffic will start going without VPN protection. This isn’t ideal if you need the advanced killswitch functionality. However, it does work properly provided the client is actually running.
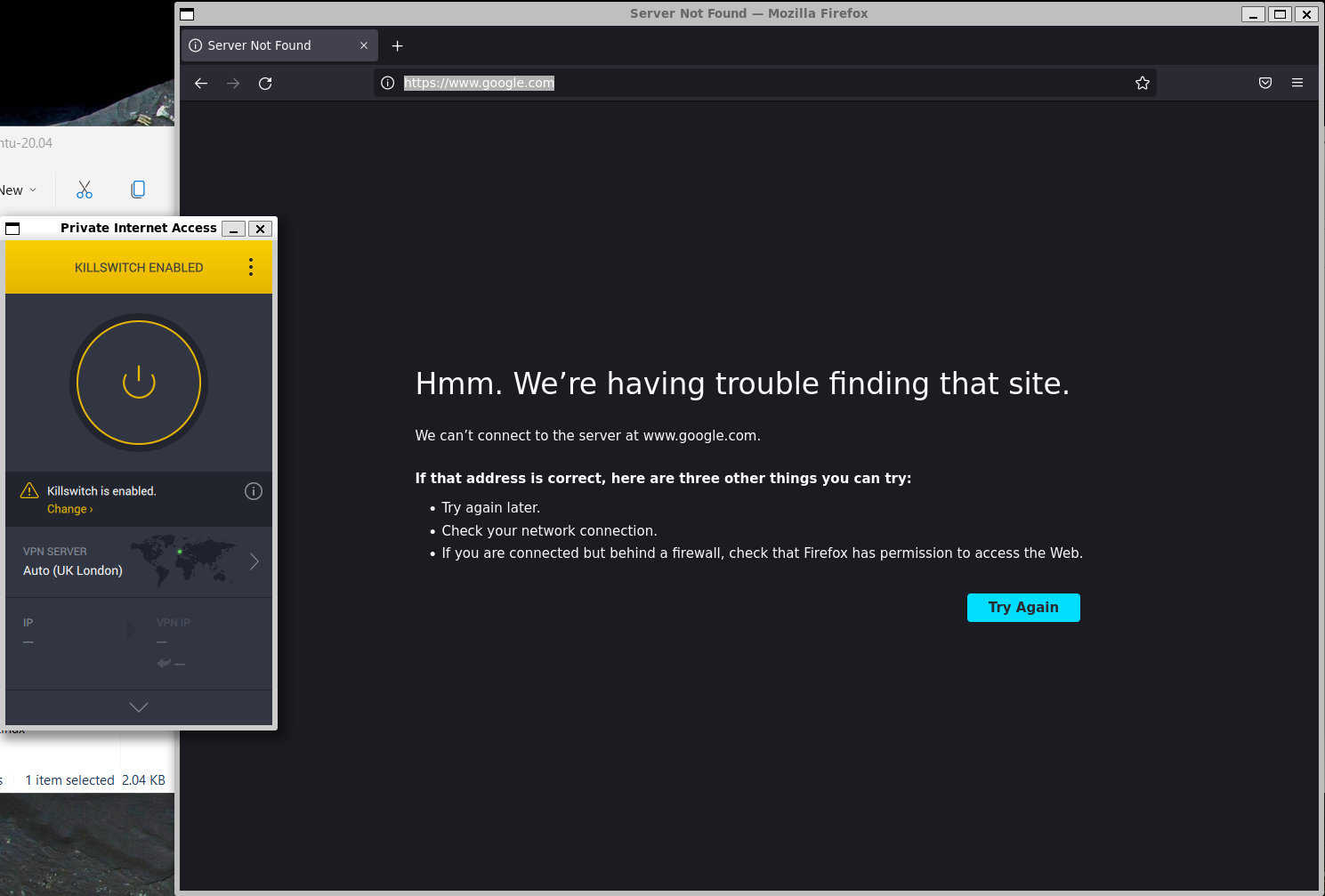
But doesn’t appear to if client crashes or is exited.
This may be something I’ve just not set up properly though, possibly to do with IPTABLES.
If you’ve enjoyed this post and found it helpful – or indeed otherwise – please leave a comment below and let me know. Thanks for reading!
Featured Image by Dan Nelson from Pixabay (with some small modifications)


